bps_user account
Applies to version: 2022.3.x and above; authors: Jacek Język, Krystyna Gawryał
Introduction
WEBCON BPS version 2022 R3 comes with a dedicated database read account. During each new installation, a database account named bps_user is automatically created in all Content databases, which is used by BPS to read data from the database.
In contrast, when upgrading the system that is already running, bps_user will also be created, but it will only be used if the system previously used a dedicated database read-only account (the ability to use such an account was optional in versions up to and including 2022 R2). If a database read-only account has not been configured, after the upgrade communication with the database will take place as before (without using the bps_user account).
This article aims to take a closer look at the application of this account, its privileges and associated limitations.
Scope of application
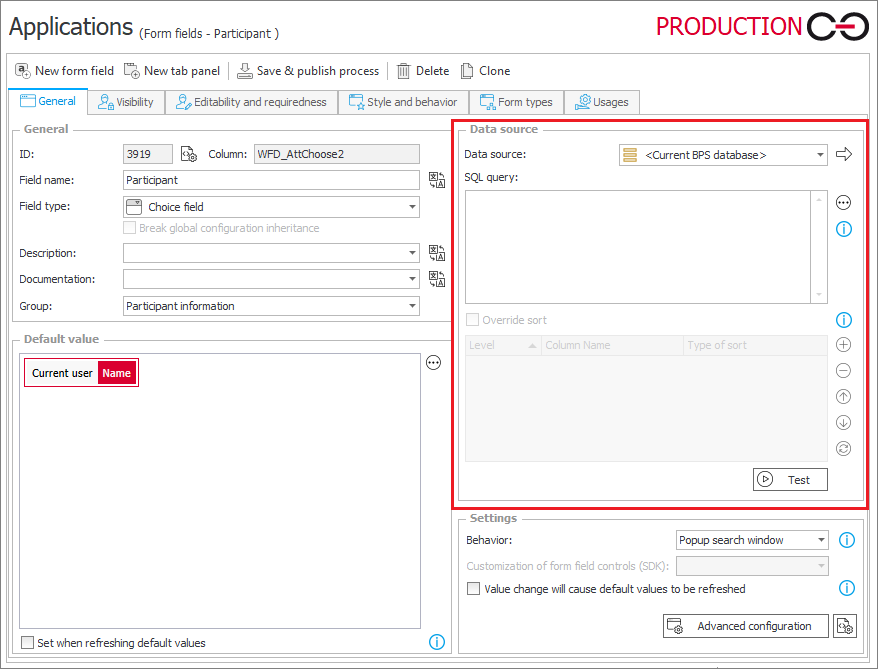
The ability to add a dedicated account for reading data from the database already existed in earlier versions of the system, but now it is created by default. Thus, bps_user is the standard account in the context of which SQL COMMAND rules and all queries using the Default connection are executed, e.g. when configuring selected form fields or actions, executing or testing SQL queries with the use of <Current BPS database>.
If the system is upgraded to the latest version, all queries executed so far in the context of the dedicated Database read account will be executed in the context of bps_user by default, and this behavior cannot be changed.
Privileges and limitations
The bps_user account has select type privileges, so they can only read data from strictly defined tables.
The scope of data access has been defined to enable full freedom to configure processes and applications, taking into account business data stored in the database, while blocking access to tables storing strictly technical and configuration information.
The bps_user is allowed to read from tables storing data of instances and dictionaries, information about attachments, tasks, companies, currency exchange rates, translations. They can also read parts of tables that store configurations of applications, processes, workflows, steps, forms, actions.
The full list of granted accesses for bps_user can be found in the [dbo].[proc_GrantLowPrivileges] procedure definition.
The introduced restrictions are justified – in this way the level of data security in the system has been increased. The possibility of intentional or accidental modification of data and system configuration is thus hindered.
If, as a results of design work in the development of processes or applications, there is a need for a broader than default access to data stored in the system database, it is strongly recommended NOT to modify privileges for the bps_user account. In this case, the appropriate solution would be to create an additional database user, and then configure a connection in WEBCON BPS Designer Studio that works in the context of this user. The new connection should be used for those configuration locations that require extended access to the database.
At this point, it is worth reminding and emphasizing that any modifications of data in BPS databases (using UPDATE or INSERT commands) performed via a non-standard connection are not allowed and may cause the system to crash. For this reason, when using non-standard connections to BPS databases, it is recommended to limit user privileges to Read only.

